Used car checks is dedicated to helping ensure that you buy your next vehicle and have peace of mind that it’s not dodgy. We are currently developing our website but we do have mobile applications use the links of this page to download and use them today.
What data do you supply?
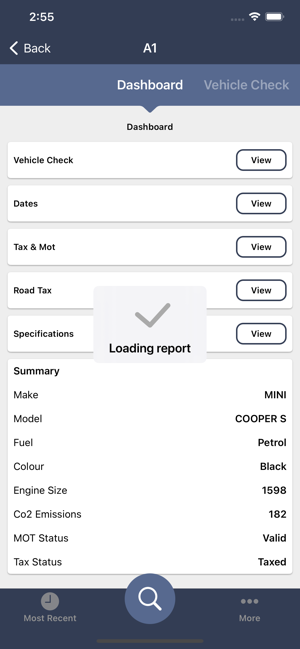
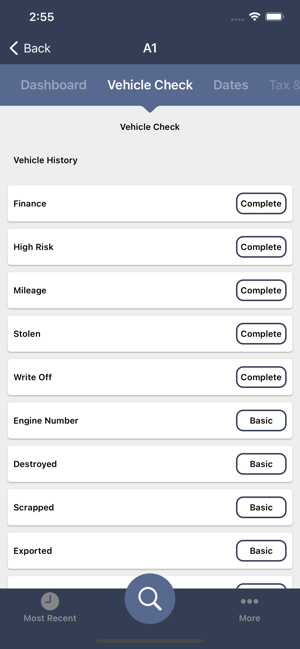
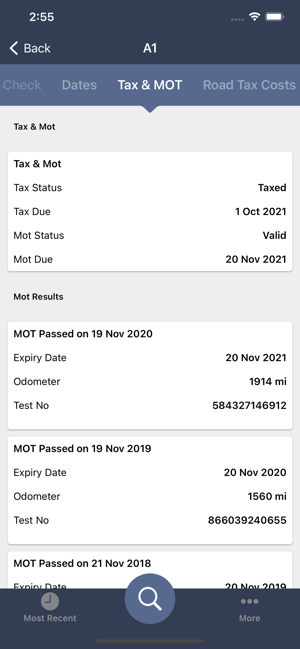
We provide checks that include but not limited to, MOT, Tax, Colour, Mileages, Important Dates, Finance, Stolen, Write-off, Scrapped and many many more.
Why Used Car Checks?
You are free to use any provider of vehicle provenance checks like HPI, Experian, AA, My Car Check, Total Car Check or others but we cannot comment on their services or vouch for them. What we can do is say that at Used Car Checks we will give you all the available data we have at hand about that vehicle, when doing your used car check. When you enter your number plate we will give you all the data required to identify the vehicle and check it’s MOT and Tax.
Can I have a Free Car Check?
There is no services that provides a free car check however for free we at Used Car Checks will provide the following data for free:
- Basic Car information – Make, Mode, Colour, Engine Size, co2 Emissions.
- MOT & Tax History.
- Road Tax Costs.
- Various other pieces of useful data insights.
We endeavour to listen to our customers so we will try to supply more data for free when possible but due to external data providers and contracts this is not always possible.
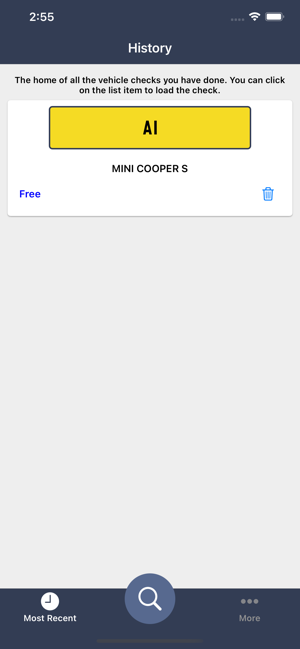
Used Car Checks on the Go!
Our mobile app is available on the Apple AppStore and Google Play Stores respectively. You can download it using the links below
Please do ensure you leave a review and if you have any problems do not hesitate to contact us.